As COVID-19 continues to put heavy strains on the Canadian healthcare system and the economy as a whole, cybercriminals are working to take advantage of exposed vulnerabilities.
Spoofed Government of Canada websites
Due to their need for guidance regarding the viral disease, Canadians have come to rely heavily on government websites. Seeing an opportunity to steal account credentials and personally identifiable information, scammers spoofed or made incredibly similar copies of official government websites, such as those of the Canada Revenue Agency and the Public Health Agency of Canada.
These malicious sites ask visitors to subscribe to newsletters — which by and large lead to phishing attacks — or have them download outbreak maps and other COVID-19-related files that are laced with malware.
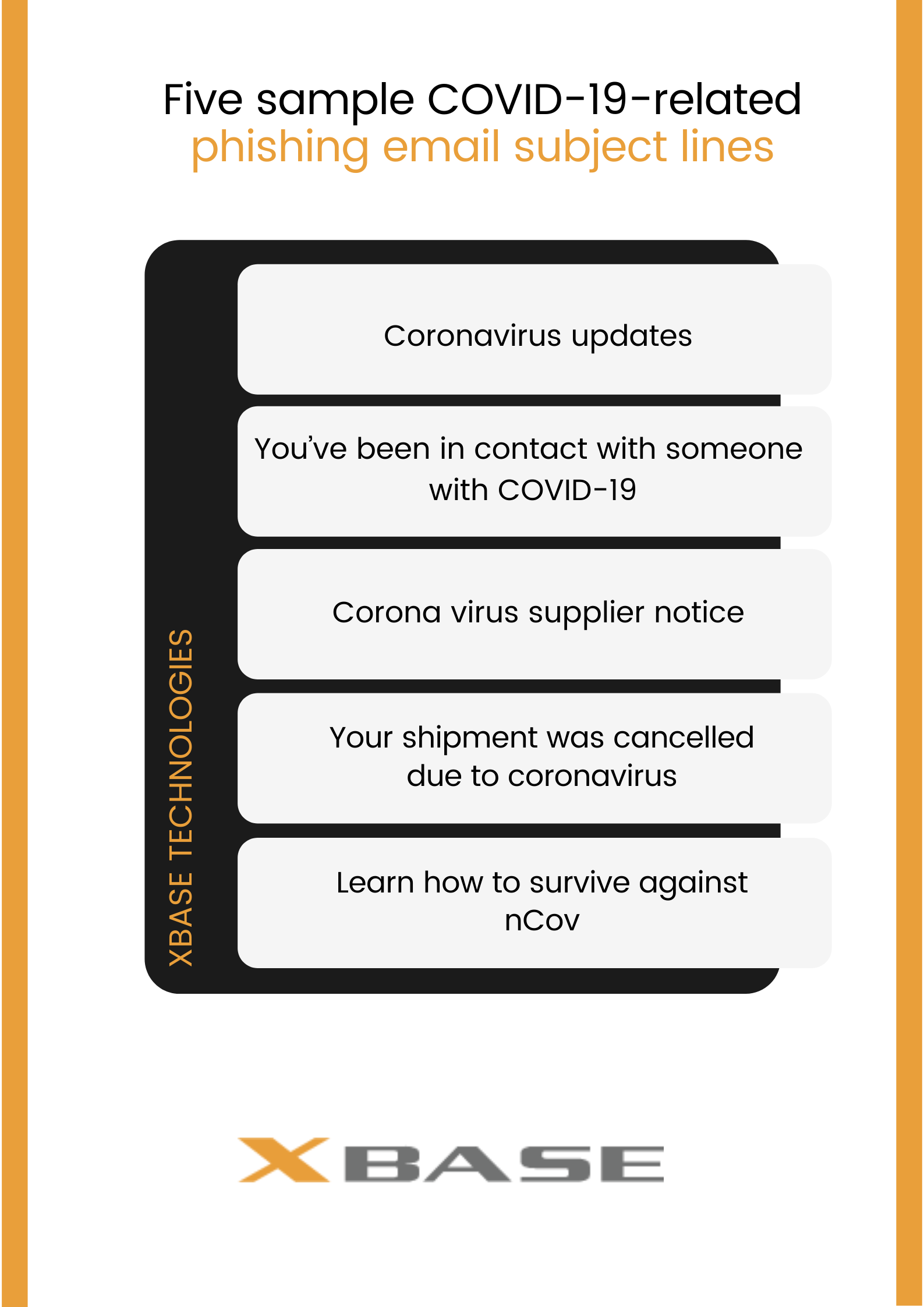
Sample COVID-19-related phishing email subject lines:
- Coronavirus updates*
- You’ve been in contact with someone with COVID-19
- Corona virus supplier notice
- Your shipment was cancelled due to coronavirus
- Learn how to survive against nCov
*Purportedly from the government or from WHO
Related article: Please be aware of COVID-19 phishing attempts
In this scenario, spoofed websites are doubly dangerous. Firstly, cybercriminals use these to steal access credentials and break into bank accounts and the like. Secondly, these sites also spread unintentionally wrong or inaccurate information (misinformation) and intentionally misleading information (disinformation) regarding COVID-19. Because of how treacherous these fake government sites are, the Communications Security Establishment is working overtime to take these down.
Healthcare institutions under siege by cybersecurity threats
Beyond having to deal with increased hospitalizations, Canadian healthcare institutions have to fend off malware and hacking attempts. This is because there’s a lot of illicit money to be made from many segments of the healthcare industry:
- End-consumers – Individuals’ health records can be worth more than credit card information to cybercriminals. Because they are unchanging and unique to individuals, healthcare records are the perfect tool for stealing identities.
- Hospitals and other healthcare providers – They depend on data to properly care for their patients and save the lives of those who are gravely injured or ill. Malicious actors are relentless in their efforts to infect hospital systems with ransomware to literally hold patients’ lives hostage.
- Medical researchers and the government agencies that aid them – Countless medical researchers around the world have agreed to set market competition aside and work together to come up with a vaccine for COVID-19. However, not all can place the value of human life above profit. According to the Canadian Centre for Cybersecurity, health organizations are at greater risk from “sophisticated threat actors” who want to steal intellectual property from Canada’s COVID-19 R&D. Moreover, the threat actors are poised to take sensitive data that agencies gathered during efforts to curb the spread of the coronavirus.
Company networks exposed to malware attacks and other threats because of remote working
While companies that can let their employees work from home have a leg up over those that can’t, they also increase the risk of infecting their networks with malware. This is because remote workers’ devices may be carrying bad software.
Related article: Remote working: Will it be the new norm?
Other threats to your remote workers and network include:
- Man-in-the-middle (MitM) attacks – When a remote worker and your corporate network communicate with each other, threat actors place themselves between the two parties and proceed to either:
- Eavesdrop, log users’ activities, and steal account access credentials and other sensitive information
- Intercept and manipulate the communications between the two parties
To launch MitM attacks, threat actors use these common techniques:
- Insertion – Diving into existing unsecured connections (such as public Wi-Fi)
- Wireless hijacking – Creating a public Wi-Fi network that poses as one offered by an establishment (such as a cafe) and lets unsuspecting users expose all of their communications there
-
Traffic manipulation – Via a particular malware in a remote worker’s mobile device, a hacker can put their traffic on top of the user’s to manipulate the flow of data and gain unauthorized access to your network.
Many businesses in Toronto and beyond trust XBASE to help them navigate today’s treacherous cybersecurity landscape. To learn more about how a partnership with us can protect your business from cyberthreats, download our eBook today.
Do you need help with your IT needs?
Like This Article?
Sign up below and once a month we'll send you a roundup of our most popular posts